
Research & Analysis

-
Blog Post
Professor Matthew Bunn's thoughts on the 80th Anniversary of the Trinity Test
by Matthew Bunn
Our Programs

The Defense, Emerging Technology and Strategy Program focuses on defense policy issues, security strategy execution, and new technologies that have emerged as pivotal to the future of international security, with a focus on space, artificial intelligence, autonomous systems, and synthetic biotech.

The Arctic Initiative integrates insights from cutting-edge scientific research, Indigenous knowledge, and policy analysis, to improve understanding of Arctic climate change; develop responsive policies and actions; and train the next generation of interdisciplinary Arctic experts and leaders.

The Middle East Initiative provides topical timely analysis on energy, diplomacy, foreign conflict resolution and more.

The Applied History Project promotes the use of historical reasoning to illuminate current challenges and choices in both the public and private sectors.

The Science, Technology, and Public Policy Program brings science and technology into the design of public policy, exploring some of the world's most challenging problems - from nuclear negotiations with Iran to privacy concerns about big data.

The Intelligence Project is building a new generation of practitioners serving a rapidly changing world, focusing on history, geopolitics, and emerging technologies, linking intelligence agencies with Belfer researchers, faculty and students to enrich education and support public policy decision-making.

The Project on Managing the Atom conducts and disseminates both timeless and topical policy-relevant research on nuclear weapons, nuclear energy, and nuclear non-proliferation and disarmament.

The Environment and Natural Resources Program examines cutting-edge issues at the intersection of environmental, climate, and science policy considerations, conducting policy-relevant research on energy technologies, grid decarbonization, hydrogen, biofuels, and climate finance.

The Geopolitics of Energy Project explores the intersection of energy, security, and international politics. The project aims to improve understanding of how energy demand and supply shape international politics – and vice versa.

The Africa Futures Project drives debate and research on critical issues of African politics and governance; climate change and the global energy transition; conflict and security; and geopolitics as they shape our collective future.

The International Security Program addresses the most pressing threats to U.S. national interests and international security, supports supports young scholars with its fellowship program and sponsors and edits the quarterly journal International Security.

This is just a sampling of the Belfer Center's research programs, projects, and special initiatives. To explore more about our various research programs, visit our Programs page.












Middle East & North Africa
-
Article
Hamas Accuses Netanyahu of Obstructing Ceasefire Deal
Jul. 11, 2025From Middle East Initiative
-
Article
Former U.S. Ambassador to Israel Breaks Down Potential Ceasefire Disagreements
Jul. 10, 2025
Artificial Intelligence
-
 U.S. House of RepresentativesTestimonies
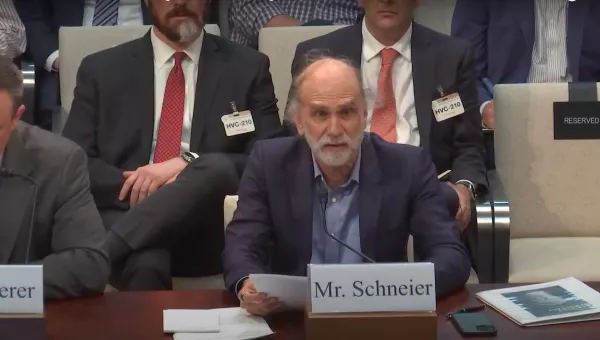
U.S. House of RepresentativesTestimoniesBruce Schneier's Testimony on "The Federal Government in the Age of Artificial Intelligence"
From Science, Technology, and Public Policy
Energy
-
Q&A
The Future of EVs: A Conversation with Elaine Buckberg
From Harvard Project on Climate Agreements
-
Policy Briefs
Harvard Project Releases Second Discussion Brief on Climate-Change and Trade Policy
May 2025 -
Reports & Papers
In the Vortex of Great Power Competition: Climate, Trade, and Geostrategic Rivalry in U.S.–China–EU Relations
April 2025
Science & Technology
-
Blog Post
Another Technology Race: US-China Quantum Computing Landscape
From Defense, Emerging Technology, and Strategy
Interest Areas
Our research spans a variety of key issues across the globe, at the nexus of science and international affairs
